Oh yes, Inception is a tool for breaking into computers with full-disk encryption; assuming you have physical access via screen-lock or a suspended state. There is a reason your told to shutdown your computer when it’s not in your possession!
One needs a FireWire interface on-board or simply, plug a FireWire card into an open slot. As the names eludes, this attack breaks into the dreams of sleeping computers – directly accessing their memory and conning secrets.

This can not be easily remedied with a simple driver update because FireWire requires direct memory access for high-speed transfers.
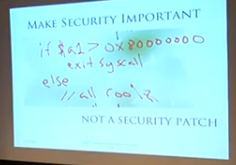
Inception’s main mode works as follows: By presenting a Serial Bus Protocol 2 (SBP-2) unit directory to the victim machine over the IEEE1394 FireWire interface, the victim operating system thinks that a SBP-2 device has connected to the FireWire port. Since SBP-2 devices utilize Direct Memory Access (DMA) for fast, large bulk data transfers (e.g., FireWire hard drives and digital camcorders), the victim lowers its shields and enables DMA for the device. The tool now has full read/write access to the lower 4GB of RAM on the victim. Once DMA is granted, the tool proceeds to search through available memory pages for signatures at certain offsets in the operating system’s password authentication modules. Once found, the tool short circuits the code that is triggered if an incorrect password is entered.
An analogy for this operation is planting an idea into the memory of the machine; the idea that every password is correct. In other words, the nerdy equivalent of a memory inception.
After running the tool you should be able to log into the victim machine using any password.